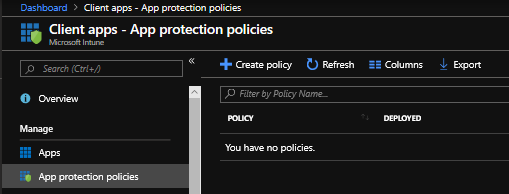
When it comes to managing data these days it can definitely get a little crazy, there are just so many ways data moves around on different devices in different apps. Keeping a close eye on everything can be tricky, but one thing to help out here is Windows Information Protection (WIP). Previously known as enterprise… Continue reading Managing Windows 10 with Intune – WIP for Office 365
Category: Intune
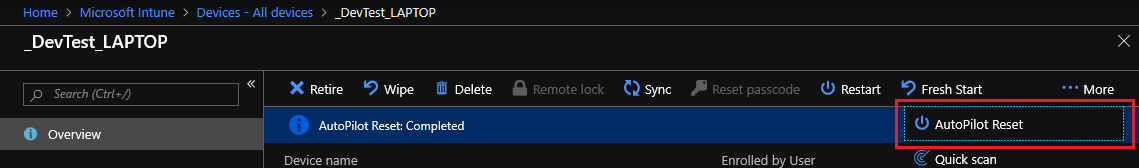
Managing Windows 10 with Intune – AutoPilot Reset
Managing Windows 10 with Intune – AutoPilot Reset Playing with the AutoPilot Reset and essentially refreshing my home laptops over and over, I thought why not just document and share it. I’m coming at this from a “Devices already managed” approach, so I did not pre-register my hardware ID’s for the full white glove experience.… Continue reading Managing Windows 10 with Intune – AutoPilot Reset